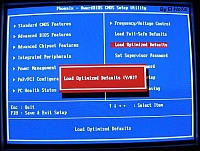
BIOS screen
The One Laptop Per Child 2B1 computers, like all PC computers, will have a BIOS to control basic computer functions. And as security patches, bug fixes, and future enhancements are made, the 2B1 BIOS will need to be updated.
OLPC is currently thinking through the process of making a BIOS upgrade that with be safe against hackers and their worm spawn, but at the same time will allow for upgrades by OLPC or even national governments.
The software developers agree they need hardware-level protection, or else worms could destroy any laptop they reached, thousands simultaneously if they were mesh-Internet connected. The prevailing idea was to require a set of physical keys to be pressed to authorize an upgrade (Ctrl+Alt+Del for example), which could still be compromised by phishing ("Hey kid, press Key 1+2+3 to download this game!").
Then at an unpleasant hour of Sunday morning, Ivan Krstić, a developer on the OLPC team had an inspiration and detailed a rather technical approach to upgrading BIOS that promised to be:
a completely secure BIOS solution which requires no TPM, allows fully automatic upgrades without the user's cooperation (such as pressing keys), and fully protects both against phishing and automated attacks -- in fact, it's vector-independent. The design also allows provisions to be made for kids that are brave enough to want to hack their BIOSes, as well as for countries which want to offer additional non-OLPC BIOSes.Ivan ended his post with a very brave call for critiques, and like DoS attack, they came fast and furious, but mostly on policy instead of the technical approach.
First up, other developers questioned the idea of automatic upgrades executed without a user's consent with commentary from the basic belief that updating a new BIOS without user knowledge is *evil* to the more detailed and persuasive:
Upgrading of firmware should always require the users explicit assent… It's too dangerous to allow automatic upgrades of the firmware, cryptographically signed or not. Do you know of any devices that upgrade their firmware without consent unless the *local* admin has explicitly chosen to enable that? I'd guess they are few and far between. If anything, maybe cable boxes and DVRs. OLPCs are not TVs.Yet, not everyone thought it was *evil* to do automatic upgrades. Some felt that requiring student's cooperation for legitimate upgrades would burden them with the need to distinguish between legitimate and illegitimate upgrades, or require adult supervision, both which could still be fooled by phishing.
Personally, I tend to believe that there can be no technical solutions to phishing, it's a problem of educating the user. Or for those who still believe PayPall email, a way to cull out the fools.
Still, Ivan new approach allows the next generation of hackers to experiment with BIOS, maybe producing a new Linus Torvalds by asking for a developer signing key. That is unless a worm author doesn't fool OLPC with "Hey, I'm a kid wanting to hack the BIOS, can I have a signing key?"
And of course there is always the ever present soldering iron, which can swap out any BIOS-containing internal component or, once quantum computing becomes reality, pure raw power encryption-cracking. Neither is part of the threat model, but Ivan successfully defended his idea against them none the less.
No matter the outcome, the process, by being open to public scrutiny and even asking for it, will produce a bios update far more secure than the current "security through obscurity" mindset. Or as Ronald Minnich says:
Score one more for open sources BIOSes!.




The developer signing keys are locked to a particular machine; a worm author who impersonates a child would be able to write a payload that maliciously replaces exactly one laptop's BIOS.
By the way, the chip image is not of our actual SPI ROM, but of a PLCC that's there for testing and development purposes.